I can’t recall the first time I used cryptography in a larp, but it was a good 20 years ago. Some players like the puzzle solving, some don’t, no-one likes struggling with something that for plot reasons is actually impossible. Tricksy.
Experience suggests the simplest cipher – the Caesar – is easily breakable in a field by anyone keen enough to bother trying. (Specifically the Caesar with a key length of 13, also known as ROT-13, is trivial to a sub-set of larpers who know that – for example – the word ‘work’ encodes as ‘jbex’.)
The Vigenère cipher is a step up. The enthusiastic can crack it with hard-skills, but it takes time and effort.
If you want something to reveal its secrets easily, use an online encoding tool and encode with ROT-13. If you want something that needs a bit of thought, use a Caeser cipher with a different key length. If you want a hard-skill challenge, use a Vigenère cipher, and if you want a soft-skill challenge, use a Vigenère cipher and give them the key and a guidebook. It’ll still take a while, but they’ll crack it.
There’s any number of online enciphering tools: this one is lovely. By default it gives you the Caeser Cipher but you can select Vignere instead.
I wrote an IC introduction to cryptography for All For One – it’s entitled “A note on ciphers“, and it’s lower down.
It misses out steganography, the art/science of hiding messages in images, or music, or whatever which Liam Spinage reminds me is fun to play with. That’s well worth a look. Must think about that.
Whatever method you end up using – the tricky bit is giving out an encrypted message that is impossible to solve without the right key, that can be solved with the right key, but all that is obvious so no-one spends ages trying to solve it pointlessly.
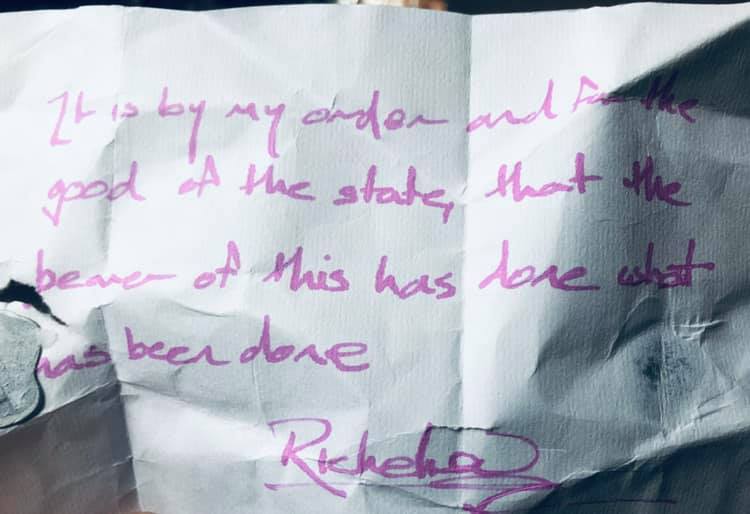
I’m sure there’s any number of ways of doing this – notably, scrawling “This is coded, get a ref to know more” on a bit of paper. However. I spent 7 or so years working in the field of cryptography, and if you can’t indulge yourself running a larp, well, where can you, so…
Please excuse a bit of nerdery I’m quite proud of…
At All For One, we wanted ciphered messages to be unbreakable until we’d hit a specific story beats, but we didn’t want to waste anyone’s time trying.
I wrote a plaintext message that indicated a scrap of in-game knowledge about the cipher, and the off game knowledge that the message was uncrackable without a specific key. Then I encoded that message using ROT-13, and used that as the in-game ciphertext so it couldn’t be easily read. However, anyone who cared to try and decrypt the message would find as quickly as I could manage that they’d not be able to. Then I ran the in-game ciphertext through a Vignere ciphering tool, with a key that had the text of the in-game message I wanted the decoded text to reveal, which I’d massaged to be the same length as long as plaintext decrypted with ROT-13, making an essentially uncrackable ciphertext which would say what I wanted it to when you used a specific key to decrypt it.
The example: messages and keys….
In-game ciphertext
ngevi vnynz bhagb sjbex gryyf lbhgu vfvfn zrffn trhfv atnpl cureh frqol gurdh rraju vpuar rqfnf crpvs vpxrl gbqrp elcgL bhjvy yabgo rnoyr gbqrp elcgg urzrf fntrj vgubh gguvf xrlgj b
Plaintext when decrypted with ROT13
a trivial amount of work tells you this is a message using a cypher used by the queen which needs a specific key to decrypt You will not be able to decrypt the message without this key two
Complex key two
bibri elkah ihnex dyxef ccefm exsvu ixitz gjrsb ttbrs ttslz ydpgt sdwxt saglh eoojw dause rdcio cenrm ebbyx vnvnv mxpcI bjnou laqvg zykyp chdol nlsyt odumx sjcqy hsria gthhj bnego x
Plaintext when decrypted with complex key two
mydea rcons tance pleas eputt hepla ninmo tionm aygod havem ercyo nours oulsa ndmay spain andfr anceg rowto loveu soned aywhe nalli speac eunde rakin goffi nerbl oodth annow wehav e
An introduction to cryptography
At All For One, characters were tagged with words that described their interaction with the world – tags ending up as a combination of skills, plot hooks and ooc game style interests. During the game, players could use their tags to enquire of a ref if they knew anything about a specific situation. Before the game, we wrote up some document for some tags with some of those answers presented as IC documents – this one was distributed to those tagged: “Well-read“.
To the best of my knowledge, it’s all true off-game as well.
A note on ciphers
Presented by a lover at court
Since the earliest times, messages have been communicated by codes and ciphers. Indeed, it may be claimed that language is itself a code. Unless you know “Zut Alors! May I have the pleasure of this dance?” has that meaning, your attempts at romance with a Frenchman are doomed to failure. The educated know the difference. A code may conceal meaning, a cipher is intended to.
To pass an enciphered message from one person to another, it is necessary that both parties know which cipher was used, and have correct ‘key’, so that the sender may encrypt it and the receiver may decrypt it.
The sender applies the key to the plain text of their message to produce a cipher text. The receiver applies the key to the cipher text to retrieve the plain text.
The Caesar cipher
The simplest cipher was used – and some say invented – by the Glorious Julius Caesar, thrice-praised conqueror of of the filthy Gauls in ancient times.
The Caesar cipher simply shifts each letter in the original message a certain number of places down the alphabet. For example, with a shift of 1, A would be replaced by B, B would become C, and so on.
For the Caesar cipher, the key is the number of characters to shift the cipher alphabet.
Here is a quick example of the encryption and decryption steps involved with the Caesar cipher. The text we will encrypt is ‘defend the east wall of the castle’, with a key of 1.
plaintext: defend the east wall of the castle
ciphertext: efgfoe uif fbtu xbmm pg uif dbtumf
It is easy to see how each character in the plaintext is shifted up the alphabet. Decryption is just as simple, each character in the ciphertet is shifted back down the alphabet.
plain: abcdefghijklmnopqrstuvwxyz
cipher: bcdefghijklmnopqrstuvwxyza
Obviously, if a different key is used, the cipher alphabet will be shifted a different amount. A common key used by those who would conceal secrets from the state is 13.
However, a Caesar cipher is easily broken with time and a sufficiently long message to study.
One common technique is to count the number of times each letter appears in the cipher text. Once you know that the most common letters are, in order, e, t, a, o, i, n, s, r, h, l, c etc, you can compare that order to the order of letters in the message and begin to build a notion of what it might say.
Alternatively, you could look for common letter combinations in the message, and match them to common words: the, be, to, of, and, in, have, that etc. Many is the agent whose careful effort has been trivially defeated by their enemies knowledge that the four-letter combination “jbex” is the cipher text for the word “work” enciphered with a Caesar cipher and a key of 13!
The Caesar cipher is no defence against attack by a rival in love let alone the competent counter-agent.
The Bellaso cipher
Some 75 years ago, Giovan Battista Bellaso of Brescia refined Caesar’s method to a cipher so fiendish as to defeat even the most skilled, and in some cases to be entirely unbreakable.
Bellaso built upon the tabula recta of Trithemius by adding a repeating key to switch shifts during the message. Bellaso’s scheme means the pattern of substitutions can be easily changed, simply by selecting a new key. Keys are typically single dates or short phrases of letters, known to both parties in advance, or transmitted in some other fashion with the message. The method thus requires strong security for only the key. As it is relatively easy to secure a short key phrase, such as by a previous private conversation, Bellaso’s system is considerably more secure.
Here is an example of the encryption and decryption steps involved with the Bellaso cipher. The first text we will encrypt is ‘the’, with a key of 6/15/21/18 – which we could alternatively articulate as “four”.
Plaintext: one for all and all for one
Cipher text: tby wtf ucq ohu fzf wtf iej
The closer the key length is to the length of the message, the closer the message is to becoming entirely unbreakable. In such cases, we recommend putting one or other of the agents involved in the communication To The Question until the key is revealed. It will usually become clear to the counter-agent that a strong cipher has been used after trivial study.
However, do be careful to check that the information you are given is accurate using other means, as in some cases different keys applied to the same ciphertext may produce different plaintexts, only one of which is the actual message.
Post-script: You will meet French who claim this cipher was invented by Blaise de Vigenère. You are to laugh at them, as this thief merely took the work of his betters and popularised it, sporting his clothes and divesting him of his labors and honors.
In the game, this document was at one point intended to be written in Italian, hence the sarcastic comments about the French. Our language rules had it that Italian text was rendered in purple text, so the players could read them, and could easily know that their characters couldn’t unless they could read Italian. Nice bit of design I first heard of from Dick Britton and the Voice of the Seraph (Crooked House, 2003), with some lovely implications elsewhere in the game.
I am reminded of an occasion when a player (skilled in the cryptographic arts to well past the average) at Odyssey confronted me at the GOD desk to complain that we were issuing props with ciphers on them that were too hard to break in a field.
The prop in question, which she waved at me to punctuate her point, was a replica of the Phaistos Disk, with it’s Linear A inscription, which as far as I know remains untranslated to this day. I didn’t have the heart to tell her.
Memory wants to believe I once sent out an RSA-encrypted message with a low bit length key. Which was defeated.
I think memory is lying to me but I can’t be sure…
Recall there’s another “midrange” Caesar Cipher: the Caesar Block transposition. Use a square matrix for greatest ease. Write the msg in a square matrix left to right top to bottom, transcribe it top to bottom,left to right. A giveaway that this is being used is if the number of letters in the msg is a perfect square, the players get really excited cracking one of these. If you want some C implimenting it, email me. Blocks provide haunting word frags brains like to fool with.